Dear Mr. Dar,
Human Rights Watch is an independent international organization that monitors human rights in more than 90 countries around the world. I am writing to request your input and perspective to incorporate into Human Rights Watch’s reporting on surveillance abuses in Ethiopia. Our reporting is based on a forthcoming report by Toronto-based research group, Citizen Lab.
We have recently learned through research conducted by Citizen Lab that several Ethiopian activists and commentators based in the United States and United Kingdom, along with one of Citizen Lab’s own research fellows, were targeted with email phishing attacks that, if successful, would have infected their electronic devices with spyware. The report also identifies dozens of other successfully infected devices belonging to unidentified targets in 20 countries. Once infected, the entity that controls the spyware would have unauthorized access to information stored on the targets’ devices. Citizen Lab’s analysis of the spyware log files for these attacks links them to Cyberbit’s PC Surveillance System (PSS) product and places the spyware’s operator inside Ethiopia. The report also identified potential product demonstrations to possible clients in several other countries, including Kazakhstan. Thailand, Uzbekistan, and Vietnam.
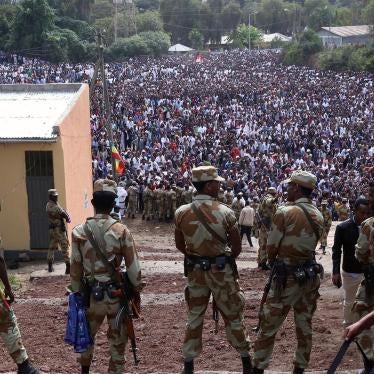
The Ethiopian government has a documented history of abusing surveillance technologies, which has facilitated a range of other human rights violations. In a 2014 report, Human Rights Watch documented how the Ethiopian government misused telecommunications surveillance systems and spyware to monitor the activities of perceived political opponents and to silence dissent and intimidate critics.[1] The report describes how Ethiopian authorities have previously used spyware products sold by two other companies, UK/Germany-based FinFisher and Italy-based Hacking Team, to similarly target journalists and government critics outside of Ethiopia. Ethiopian authorities continued to misuse Hacking Team’s system to spy on individuals abroad through at least 2015, when a widely covered breach of the company’s corporate data confirmed its business in Ethiopia.[2]
Ethiopia’s national laws lack meaningful protections for the right to privacy, and the country’s broad security and law enforcement powers are not adequately regulated to prevent arbitrary, unlawful, or disproportionate surveillance. The Ethiopian government has also long invoked national security as a pretext for clamping down on human rights. For example, in a 2015 report, we documented how the government used counterterrorism laws to target journalists and others critical of government.[3] At least 75 journalists have fled into exile since 2010.
Given this context, we want to better understand the circumstances under which Cyberbit’s product was obtained by the Ethiopian government and the steps Cyberbit takes to address any abuse of its products and services by its governmental customers, particularly government agencies seeking lawful intercept, intelligence, or offensive capabilities. We would appreciate specific replies to the following questions. This will greatly assist our understanding of Cyberbit, the products and solutions it offers, its approach to human rights risk, and how it would respond to credible reports of illegal surveillance and other human rights abuses linked to its products and services.
- What products, services, or training has Cyberbit provided to the Ethiopian government? Has Cyberbit specifically sold its PC Surveillance System (PSS), PC 360, or a similar product that enables covert information gathering from remote computers to any Ethiopian governmental agency?
- Does Cyberbit currently have any governmental clients in the other countries identified in the Citizen Lab report as locations of potential product demonstrations, including Kazakhstan, Nigeria, the Philippines, Rwanda, Serbia, Thailand, Uzbekistan, Vietnam, or Zambia?
- What policies and procedures does Cyberbit have in place to vet potential sales or governmental customers? To what extent does Cyberbit inquire about the end use or end users of its products and services?
- Has Cyberbit ever conducted due diligence with respect to sales to the Ethiopian government, particularly by examining the government’s human rights record and past surveillance abuses targeting journalists and activists (for example, using FinFisher or Hacking Team products)?
- Can Cyberbit elaborate on any policies or procedures it has in place to address and prevent human rights abuses linked with the use of its products or services by governmental customers?
- How does Cyberbit monitor whether governmental customers are complying with the terms of their contracts or otherwise misusing its products? What steps, if any, does Cyberbit take if it uncovers violations of company contracts or the use of its products to facilitate human rights abuses by its customers?
We would appreciate a response by December 5, 2017 in order to reflect your response, as well as any other perspectives you may wish to share, in our reporting.
Thank you for your consideration and we look forward to your responses to our inquiries. We would also welcome the opportunity to discuss these issues with you further.
[1] Human Rights Watch, “They Know Everything We Do”: Telecom and Internet Surveillance in Ethiopia, March 25, 2014, http://www.hrw.org/reports/2014/03/25/they-know-everything-we-do.
[2] “Ethiopia: Digital Attacks Intensify,” Human Rights Watch news release, March 9, 2015, https://www.hrw.org/news/2015/03/09/ethiopia-digital-attacks-intensify; “Ethiopia: Hacking Team Lax on Evidence of Abuse,” Human Rights Watch news release, August 13, 2015, https://www.hrw.org/news/2015/08/13/ethiopia-hacking-team-lax-evidence-abuse.
[3] Human Rights Watch, “Journalism Is Not a Crime”: Violations of Media Freedoms in Ethiopia, January 22, 2015, http://www.hrw.org/reports/2015/01/21/journalism-not-crime.