Summary
Increasing government use of commercial spyware and other types of surveillance technology poses a significant threat to human rights worldwide. Police and intelligence services in many countries use such technology to target activists, journalists, humanitarians, academics, and other critical voices, undermining democratic institutions, shrinking civic space, violating victims’ privacy and other rights and, in many cases, threatening their physical security.
The European Union (EU), whose member states are home to many of the companies that develop and export such technologies worldwide, is part of the problem. Despite a regulatory framework designed in part to prevent abuses, the EU currently is doing too little to prevent sales and transfers from its member states to governments with a track record of using such technologies for crackdowns on dissent and other serious rights violations. Particularly for human rights defenders, journalists, and others whose work focuses on exposing abuse, corruption, and other crimes in both the public and private sectors, surveillance technology has been used to compromise their ability to work freely, safely and to protect their sources.
EU-produced surveillance technology is in use in dozens of countries worldwide as well as by countries in Europe, and the EU hosts many of the surveillance companies working worldwide: the majority of EU member states have at least one surveillance technology company operating inside their borders. In a 2024 report by Google’s Threat Analysis Group on the commercial surveillance industry, all but of the two companies mentioned are based in the EU.
In 2021 the EU passed a landmark recast of a previous law, the Dual-Use Regulation (also commonly referred to as “Recast”), intended in part to rein in the export of dual-use technology (technologies that may be used for both civilian and military purposes), including commercial surveillance technology. The new controls on surveillance technology had three key elements: an expanded harm-based definition of what products constitute surveillance technology and are subject to the regulation, including a catch-all clause requiring companies to seek licenses for the potential export of non-listed surveillance technology that meets the definition; a requirement that exporting countries consider the human rights record of destination countries and any potential for abuse; and a reporting and transparency requirement that EU member states collect data on their exports of cybersurveillance items and transmit it to the European Commission for inclusion in an annual public report. These provisions were intended to strengthen oversight and prevent the export of surveillance technologies to countries where they could be used to perpetrate or contribute to human rights violations.
This report assesses how these reforms are functioning in practice. Our analysis of European Commission public reports and data obtained via transparency (or Freedom of Information or Access to Documents) requests shows serious defects in the EU’s current approach. One problem is with the Recast itself: it does not go far enough. In particular, the requirement that EU member states to “consider” the human rights record of an export destination is insufficient to prevent exports to destinations where they are likely to be used to violate rights, as are human rights due diligence measures for surveillance companies. Another problem, the focus of this report, is that rights-protective features of the Recast, albeit with their limitations, have been undercut by guidelines developed by the European Commission to interpret the application of the regulation. These guidelines, published in January 2024, severely limit the value of the Recast’s reporting and transparency provisions. The result is that EU member states have continued to export dangerous surveillance technology to countries where it has likely contributed to abuses.
This report is divided into four sections. The first recounts the origins and objectives of the Recast, the latter notably including preventing exports of cyber-surveillance items that are likely to be used in ways that violate international humanitarian law (IHL) or human rights law. It details relevant provisions of the Recast and statements officials made about the rights-protective provisions when the Recast was adopted. It also summarizes weaknesses of the Recast from a human rights perspective. This section draws in part on prior work by Human Rights Watch and others.
The second section focuses on the non-legally binding guidelines published in January 2024 by the European Commission to support the implementation of the Recast. It details how the interpretation has hollowed the rights-protective promise still contained in the Recast. A key conclusion is that the transparency requirements of the Recast, as put into practice through the January 2024 guidelines, are so weak that what is reported by the European Commission does not allow for meaningful assessment of whether, in practice, the regulatory framework is meeting its human rights objectives. As a result of that weakness Human Rights Watch had to resort to freedom of information requests at national level of EU states to try to identify exports of concern and assess whether abusive exports are happening.
The third section describes the results of Human Rights Watch efforts—through freedom of information requests to every EU member state—to flesh out the limited information publicly reported by the European Commission under the Recast. One finding is that EU member states routinely export surveillance technology to destinations with well-documented histories of human rights violations. We highlight two illustrative examples that identify such transfers: exports of surveillance technology from Bulgaria to Azerbaijan, and from Poland to Rwanda.
Another finding is that freedom of information requests are able to fill in only a fraction of the gaps in current reporting. This is due in part to incomplete member state responses to such requests, but also significantly to overly sweeping European Commission and member state invocations of exemptions to transparency, such as trade secrets, national security and protecting international relations, as justifications for withholding information, limitations not supported by the language of the Recast itself.
The fourth section sets forth relevant international human rights standards.
The European Commission will launch an evaluation of the recast Dual-Use Regulation in September 2026. To show it is serious about the purposes articulated when the Recast was adopted, the EU institutions—Commission, Parliament and Council—should use this opportunity to strengthen due diligence and transparency requirements to ensure the EU finally curbs its export of surveillance technology to abusive governments around the world.
Recommendations
To all European Institutions
Due Diligence
Require exporters of surveillance technology to undertake a meaningful due diligence process that includes a thorough risk assessment of the possible use of their product in particular to facilitate or contribute to violations of international human rights and humanitarian law and require that the process and findings be published.
Require exporters to expressly notify member states of listed cybersurveillance items if they identify risk or find evidence of possible misuse through their due diligence process.
Clarify how the guidelines on dual-use licensing interact with the revised Corporate Sustainability Due Diligence Directive (CSDDD) which covers dual-use items until the export-licensing process.
Clarify state responsibilities if they chose to provide a license while red flags have been raised.
Revise sections of the Commission guidelines implementing the Dual-Use Regulation that relate to respecting human rights obligations in the context of dual-use licensing and due diligence so they align with due diligence standards as defined in the CSDDD (obligation of means). The revised guidelines should also define criteria to apply to all applications to export cybersurveillance technology, listed or not, from EU member states and clarify which are mandatory under either law.
Member states and/or companies should also establish mechanisms to provide an effective remedy for human rights violations committed using the transferred technology, and the use and impact of these mechanisms should be regularly reported to the relevant EU institutions.
Transparency
Update guidelines on transparency reporting on exports of dual use surveillance technology with input from stakeholders. At a minimum the guidelines should:
Require member states to report the number of license applications for both listed and unlisted technology, with at least the following information per application: the exporter name, a description of the end user and destination, the value of the license, and whether the license was granted or denied and why.
Establish explicitly that the reported information described above is public and can be provided in response to transparency requests, and that the information is not subject to article 4 exemptions under EU Regulation 1049/2001.
Initiate the evaluation process mandated by article 26(4) of Regulation 2021/821 within the required timeline, and ensure that that process provides for meaningful participation of all relevant stakeholders, including human rights and other civil society organizations.
To EU Member States
National export licensing authorities should take into account the human rights record of recipient countries and end-users (whether they be state or non-state actors) and act upon findings or red flags by withholding export licenses of cybersurveillance technology.
National authorities should report on the implementation activities with regard to due diligence responsibilities and obligations and encourage all companies to inform the public about the scope, nature, and transferable findings of the human rights due diligence procedures they implemented.
National authorities should comply with transparency and access to documents laws regarding requests for export data, and not invoke sweeping exemptions to transparency, such as trade or defense secrets, national security, or protecting international relations.
Methodology
This report is based on research conducted between November 2024 and February 2026. Human Rights Watch sent freedom of information requests to export license authorities in each of the 27 EU member states, as well as to the European Commission, asking for licensing data as reported by member states to the European Commission for the preparation of the annual report called for by article 26 of the recast Dual-Use Regulation. The language of these requests followed the language of the Recast, requesting information on export licensing of cybersurveillance items, including the number of applications received by item, destination, and the decision taken on those applications.
Depending on the country, freedom of information requests went to interior ministries, foreign ministries, or other institutions specifically responsible for dual-use export licensing. In most cases where export authorities initially denied access to the requested information, Human Rights Watch exhausted the available national appeals mechanisms for this data.
Human Rights Watch is publishing the raw data received online at github.com/HumanRightsWatch/EU-surveillance-export-data.
We also analyzed the parts of the 2021 Recast that relate to “cybersurveillance items,” as well as two sets of guidelines issued by the European Commission on transparency reporting and the definition of cybersurveillance items to assess how European institutions are implementing the elements of the regulation that pertain to human rights due diligence and transparency obligations of EU institutions and member states. Human Rights Watch also spoke at length with more than a dozen experts on export controls and the EU legislative process that led to the Recast, surveillance technology proliferation and the right to privacy.
Human Rights Watch wrote to the European Commission, export license authorities and relevant ministries in Bulgaria, Poland and Sweden, state security services and relevant ministries in Azerbaijan, India and Rwanda, as well as to the companies Circles and MSAB on April 13th and 15th. We received written responses from the European Commission and from the ministries of Economy and Industry and of Economic Development and Technology in Bulgaria and Poland, respectively, as well as from the Inspectorate of Strategic Products (ISP), the Swedish authority responsible for export controls of most dual use items and have reflected relevant parts of those responses in the report. The responses are available in full in Annex I, Annex II, Annex III and Annex IV.
This is an ongoing piece of research: Human Rights Watch, alongside partner organizations, is developing a civil society monitoring mechanism to continue requesting this data from EU member states and the European Commission and to continue carrying out local research in countries that receive EU-developed surveillance technology.
The Origins of the Recast, Key Provisions, Weaknesses
The Road to the Recast
EU countries have a long history of exporting surveillance technology to governments that use it to violate rights.[1] In the early 2010s, security researchers began documenting cases of European-developed spyware being used in countries with poor human rights records.
In 2013, researchers found evidence that Gamma International’s surveillance software, FinFisher, which can target mobile phones to obtain contacts, text messages, emails, locations, photos and other data, and to record calls, ended up being used by governments in Egypt, Bahrain, Turkmenistan, and Myanmar, among other countries.[2] Gamma International at the time denied that the identified products were from the FinFisher line.[3] In 2014, Human Rights Watch documented the Ethiopian government’s use of both FinFisher and Italy-based company Hacking Team’s Remote Control System (RCS) spyware, which provides access to computers and smart phones in real time, against opposition group members and journalists overseas.[4] In 2012, security researchers also found that the United Arab Emirates (UAE) used both companies’ software to target the high-profile Emirati activist Ahmed Mansoor, who is serving an abusive 15-year sentence.[5] Four executives from the French firm then known as Amesys, which later became Nexa Technologies, were indicted in 2021 by a Paris court for “complicity in acts of torture” related to their spyware’s role in facilitating human rights abuses in Libya and Egypt in the late 2000s and early 2010s.[6] These cases are still ongoing, and the executives have denied the charges.
At the time, the EU framework for controlling the trade in dual-use items was the 2009 EU Dual-Use Regulation (428/2009), which incorporated the control list of the Wassenaar Arrangement, an international export control regime regulating the export and transfer of weapons and dual-use items.[7] At the time, the Wassenaar list of regulated items did not include specific categories of cybersurveillance technology.
One of the first attempts at regulating global surveillance industries was a 2013 update to the Wassenaar Arrangement to cover “intrusion software” and “network surveillance systems.”[8] This came after revelations of the use and misuse of EU-exported surveillance technology by security forces in countries in North Africa,[9] and a pressure campaign by a coalition of privacy and human rights organizations, including Human Rights Watch.[10]
The change to the Wassenaar control list meant that exporters of intrusion software and network surveillance systems would need to apply for licenses from participating national governments in order to sell or transfer them. While an important first step, this classification has had limited ability to actually restrict the sale and transfer of surveillance technology. The Wassenaar Arrangement is not legally binding and is limited to the 42 participating governments. It is up to each national regulator to decide if and how to enforce it, and laws governing surveillance exports vary substantially from country to country.
In 2011, the EU began the process of updating its export control regime, as mandated by the 2009 Dual-Use Regulation. This change became increasingly important as more cases became known of surveillance technology developed in EU countries being used to violate rights.
The European Parliament has also pushing for these changes. A 2012 report by the Parliament’s Committee on Foreign Affairs called on the Commission to submit a proposal for a new regulation:
requiring increased transparency and accountability on the part of EU-based companies, as well as the disclosure of human rights impact assessment policies, with a view to improving the monitoring of exports of ICTs, products and services aimed at blocking websites, mass surveillance, tracking and monitoring of individuals, [and] breaking into private (email) conversations or the filtering of search results…[11]
A 2015 European Parliament resolution noted that EU-based companies at the time made up an important share of the global market in exports of “surveillance, tracking, intrusion and monitoring technology.”[12] The resolution called on the European Commission to propose new policies to limit and regulate dual-use technology.
In 2016, the European Commission issued a legislative proposal for what would eventually become the recast Dual-Use Regulation.[13] The proposal noted that European surveillance technology had been exported to repressive governments and conflict areas where it was used to target dissidents and human rights activists, and for other forms of internal repression. The proposal emphasized that
the export of cyber-surveillance technology under such conditions poses a risk to the security of those persons and to the protection of fundamental human rights, such as the right to privacy and the protection of personal data, freedom of expression, freedom of association, as well as, indirectly, freedom from arbitrary arrest and detention, or the right to life.
The Commission’s legislative proposal also included a plan to provide transparency on export controls through the publication of annual reports, which would, according to the document, “enable civil society organizations to fully contribute to the formulation and implementation of export control policy.” The role of transparency in increasing public awareness and facilitating work by civil society organizations was framed by the document as an important mechanism for public accountability surrounding these exports.
Following years of negotiations between the European Commission, Council, and Parliament, in May 2021 the EU passed landmark new legislation further regulating EU member states’ export of dual use items, and, in particular, certain especially harmful types of surveillance technology. The new regulation came as news began to break in July 2021 that Pegasus spyware, developed and sold by the Israel-based company NSO Group, had been used to surveil dozens of journalists, human rights activists and others around the globe. In response, the EU institutions formed a committee to investigate the use of Pegasus and other types of surveillance technology, and began working with journalists and civil society organizations to further document cases of harm.
This regulation, Regulation 2021/821, better known as the 2021 recast Dual-Use Regulation (“Recast”), entered into force on September 9, 2021.[14] According to the implementation schedule included in the regulation, the Commission is due to begin evaluating the Recast in September 2026, although in a written response to Human Rights Watch the Commission said that they would be starting the process as early as May 2026.
At the time the Recast was adopted, civil society organizations raised concerns that it did not go far enough in preventing EU member states from exporting surveillance technology to countries where they were likely to be abused.
The Recast established three important regulatory and transparency norms in the EU specific to these export licenses:
The Recast, using a definition that centers a technology’s potential for harm, expanded what types of cybersurveillance exports are regulated, including through a provision known as the “catch-all” clause[15] for surveillance technologies not included in the Wassenaar control list. In the past, export regulations only applied to the specific surveillance technologies included in the control list of the Wassenaar Arrangement.[16] This meant that cutting-edge technologies could be left unregulated until they were added to the Wassenaar control list.
The Recast also created a public reporting responsibility for the European Commission. It requires the Commission to collect data from EU member states on the exports of certain types of surveillance technologies, and annually publish a report to the Parliament and Council outlining specific elements of that data, including the number of license applications received, the type of technology concerned, and the destination for export, as well as the final decision taken on each application. The Recast also specifies that the report be public.
The Recast makes explicit the need for exporting countries to consider the human rights record of recipient countries when considering an export license application, based on criteria included in the EU Common Position. The latter is a set of common rules among EU member states that seeks to limit the export of European weapons and dual-use technology to places where they might be used for “internal repression or international aggression or contribute to regional instability.”[17]
Centrality of Transparency for Ensuring Surveillance Exports do not Contribute to Rights Violations
A stated aim of the Recast is “maintaining robust legal requirements with regard to dual-use items, as well as … strengthening the exchange of relevant information and greater transparency.” It also notes the specific importance of controlling the export of surveillance technologies given “the risk of them being used in connection with internal repression or the commission of serious violations of human rights and international humanitarian law.”[18]
Throughout the legislative process, greater transparency on surveillance and other dual-use exports was highlighted as an important mechanism for public accountability. In a 2018 Parliamentary debate on the legislation, MEP Bernd Lange noted that providing public transparency on exports was a priority for the new regulation:
Nowadays, hardly anyone knows which applications are submitted, which exports are approved, and which are prohibited. Sometimes you can find this out through parliamentary inquiries – sometimes there are leaks. We want this information to be made public on a mandatory quarterly basis. That will already have an impact on practice.[19]
Similarly, MEP Markéta Gregorová noted in a 2021 Parliamentary debate, two months before the Recast was passed: “The new rules for cyber-surveillance exports, paired with companies’ new due diligence requirements and meaningful transparency, will together mean that powerful European cyber-surveillance technology does not end up in the hands of dictators and authoritarians.”[20]
MEP Gregorová, rapporteur for the European Parliament committee responsible for drafting the Recast, described the role envisioned by civil society and journalists in monitoring for misuse. “In this regard, I also cannot omit the current and future role of civil society…. Watchdogs and non-governmental organizations and journalists always had a crucial role in the identification of problematic companies and areas. We now free their hands with the new transparency provisions to access necessary information.”[21]
Article 26 of the Recast also states that the European Commission and Council are responsible for developing guidelines for member states to use in their data gathering under the article.[22] In January-February 2023, the European Commission held a public consultation related to the development of these guidelines. In the webpage announcing the consultation, the Commission noted that the Dual Use Regulation mandates the collection of certain export data “for reasons of effectiveness, consistency and transparency.”[23] The results of that consultation, whose respondents were largely from industry, civil society and academic institutions, noted the importance of providing transparency on dual-use exports, particularly cybersurveillance items, in particular as relates to the type of item to be exported and the end-user and its end-use.[24] At no point does the document summarizing responses to the consultation mention concerns over commercial secrecy or otherwise relating to the public nature of this information. Rather, the Commission notes this input from civil society respondents:
… reporting detailed information about exports of dual-use items and technologies can enable stakeholders get better oversight of how the controls that Member States have in place are being implemented. Reporting on enforcement measures can also offer a better picture of the way in which export control violations are being detected, investigated, and prosecuted in the EU.
Promoting transparency in the trade of cyber-surveillance technologies and applying relevant exceptions to disclosure strictly - is considered critical to ensure these items are not being used in third countries in connection with internal repression or the commission of serious violations of international human rights and humanitarian law.[25]
As detailed below, these guidelines were published in January 2024 in a non-legally binding document that also includes example spreadsheet forms that EU member states were to use for their reporting of cybersurveillance export data.[26] Between the Recast coming into effect and publication of this report, the Commission has published three reports assessing its implementation and one “statistical update” document with additional export data. While all the reports contain aggregated EU export data relating to cybersurveillance items, only two of them were published after the European Commission issued its guidelines in January 2024.
The Types of Cybersurveillance Technology Controlled Under the Recast
The Recast specifically regulates six categories of cybersurveillance technology, transposed from the Wassenaar Arrangement control list, and included the “catch all” clause for non-listed technology. In October 2024 the European Commission released a second set of guidelines related to exports for cybersurveillance items, which sought to define the specific types of surveillance technology that are categorized and controlled by the Recast, as well as to explain to companies the criteria under which the catch-all clause would apply to a possible export.[27]
The Recast defines cybersurveillance technology as “dual-use items specially designed to enable the covert surveillance of natural persons by monitoring, extracting, collecting or analyzing data from information and telecommunication systems.”[28] Cybersurveillance guidelines issued in October 2024 clarify this definition and define listed export controls for six types of surveillance technology: telecommunication interception systems, internet surveillance systems, intrusion software (and related controls), communication monitoring software, items to perform cryptanalysis and forensic or investigative tools.[29]
The six categories of technology included in the October 2024 European Commission guidelines are:
Telecommunications interception systems: equipment that intercepts communication and metadata of these communications (such as phone numbers or identifier of subscribers) transmitted over wireless communications. This includes, for instance, IMSI catchers that intercept mobile phone traffic.
Internet surveillance systems: equipment that allows an operator to analyze, extract and index large amounts of Internet traffic (content and metadata) on the networks of a telecommunications carrier. These tools allow users to search in the indexed data for personal identifiers or map relational networks of a person or group of people.
Intrusion software: software that allows operators to covertly and remotely access electronic devices, in order to obtain data, track users or eavesdrop using a device's built-in microphone or cameras.
Communication monitoring software: software designed for monitoring and analysis by authorized law enforcement authorities of data collected in targeted interceptions from telecommunications providers. This software uses data collected by telecommunication interception systems and allows for searches of communication content and metadata.
Items to perform cryptanalysis: software or equipment used to bypass or defeat device locking and/or encryption.[30]
Forensic or investigative tools: equipment or software used to extract (and often analyze) raw data from electronic devices by bypassing its security controls, in many cases via a physical, cabled, connection to the device.
The October 2024 European Commission cybersurveillance guidelines also set forth criteria for assessing whether technologies not specifically listed in the Recast nonetheless fall within the scope of its catch-all clause and require an export license from a national authority. One important consideration is whether the technology in question can be used “in connection with internal repression and/or the commission of serious violations of human rights and international humanitarian law.” The guidelines include examples of potential non-listed technology that would fall under this category and, per the document, “may warrant potential vigilance” under the Recast. Examples of potential non-listed technology are facial and emotion recognition technology, location tracking devices, and video surveillance systems.
Recast Weaknesses: Due Diligence Provisions Fall Short on Paper and in Practice
Although, the preamble of the Recast explicitly refers to the need for exporting countries to consider the human rights record of recipient countries when assessing an export license application, the operative text itself lacks a reference to the internationally established framework of “human rights due diligence”. Nor does it establish any reporting mechanism to monitor how national export licensing authorities operationalize the Recast’s due diligence obligations and the standards that exporting companies were expected to apply.
The Recast does however reference the 2008 EU Common Position, a set of common rules among EU member states that sought to limit the export of European weapons and dual-use technology to places where they would be used for “internal repression or international aggression or contribute to regional instability.”[31]
The Common Position, for the first time in the European Union, sought to ensure military and dual-use export controls prevented use of exported technologies by recipient countries to commit human rights violations, and the text of the Recast makes reference to these same human rights obligations. The Common Position requires that EU member states deny an export license if there is a “clear risk” that the item to be exported might be used in violation of IHL or for internal repression, and that member states “exercise special caution and vigilance” in issuing licenses to countries where UN or European institutions have documented serious violations of human rights.[32]
The Recast provides in the preamble that EU institutions and member states are to “fully take into account all relevant considerations,” including the Common Position and other international obligations when determining whether or not to issue an export license.
Specifically regarding cyber-surveillance items, the preamble states that member state authorities “should consider in particular the risk of them being used in connection with internal repression and the commission of serious violations of human rights and international human rights law”.[33]
Article 15 of the recast Dual-Use Regulation also explicitly references the Common position imposing a legal obligation on member states “in deciding whether or not to grant an authorization or to prohibit a transit" to “take into account all relevant considerations” including international obligations and commitments, national foreign and security policy covered by the Common Position and intended end use and risk of diversion.
As noted above, article 5 also includes a so-called “catch-all clause,” requiring export authorizations for cybersurveillance items even if the technology is not specifically listed as requiring regulation if they “are or may be intended, in their entirety or in part, for use in connection with internal repression and/or the commission of serious violations of human rights and international humanitarian law.”[34] Article 5 puts much of the burden on the exporter to notify the competent authority of the human rights risk based on their own human rights due diligence and request a license, which is not in their interest to do.
This catch-all clause relies on exporting companies to carry out due diligence limited to “transaction-screening measures,” which are defined and elaborated on in the October 2024 cybersurveillance guidelines.[35] The cybersurveillance guidelines call on, but do not require, exporters to review how end-users intend to use the products, and assess whether or not their products could be used, or form a part of system used to
commit internal repression, violate or abuse human rights, including the right to life, freedom from torture, inhuman and degrading treatment, the right to privacy, right to freedom of speech, the right to association and assembly, the right to freedom of thought, conscience and religion, the right to equal treatment or prohibition of discrimination or the right to free, equal and secret elections.
This section of the cybersurveillance guidelines outlines a series of example red flags that exporters should, but are not required to look for, and if encountered, should inform national authorities, mostly related to the potential or past use in connection with serious violations of human rights, IHL, or in violation of national laws. These red flags, which, according to the cybersurveillance guidelines, “indicate that the export may be destined for an inappropriate end-use, end-user, or destination.”
While the recast does not compel exporters to search for risks, some national authorities recommend that they do so. An informational leaflet on article 5 of the Dual-Use Regulation printed by the German export authority, the Federal Office for Economic Affairs and Export Control (BAFA), states that “exporters should not deliberately ignore apparent indications; it is improper and may be tantamount to awareness to willfully look away and intentionally pass up a seemingly obvious opportunity to take note of something which any other in such position would have perceived. The complete failure to perform due diligence is improper ("passivity does not protect").”
It is a positive that the Recast text and both the January and October 2024 European Commission guidelines contain language mentioning human rights and due diligence considerations for exports, but as the Commission annual reports and member state export data reveal, the due diligence requirements are not strong enough to prevent the export of surveillance technology to governments who are likely to abuse it.
European Commission Interpretation of the Recast Sells Short its Rights-Protective Promise
The January 2024 European Commission Guidelines Redefine Transparency
The European Commission has reinterpreted the recast Dual-Use Regulation’s transparency obligations in a manner that has undermined the purpose of the regulation, and transparency reports to date do not provide sufficient detail to facilitate the scrutiny necessary to assess whether the regulation is having its intended effect.
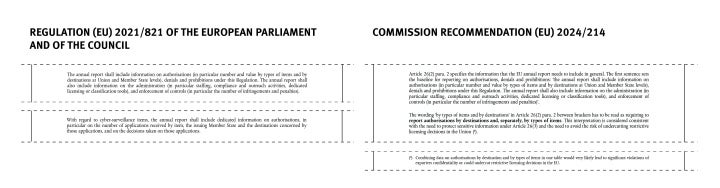
Article 26(2) of the Recast states:
The Commission shall, in consultation with the Dual-Use Coordination Group, submit an annual report to the European Parliament and the Council on the implementation of this Regulation, and on the activities, examinations and consultations of the Dual-Use Coordination Group. That annual report shall be public.
The annual report shall include information on authorisations (in particular number and value by types of items and by destinations at Union and Member State levels), denials and prohibitions under this Regulation. The annual report shall also include information on the administration (in particular staffing, compliance and outreach activities, dedicated licensing or classification tools), and enforcement of controls (in particular the number of infringements and penalties)
With regard to cyber-surveillance items, the annual report shall include dedicated information on authorisations, in particular on the number of applications received by item, the issuing Member State and the destinations concerned by those applications, and on the decisions taken on those applications…
The Recast defines transparency on cybersurveillance exports as providing information regarding the types of technology EU member states are exporting and the countries to which that technology has been sold. This is consistent with the type and degree of transparency called for in the legislative proposal as well as statements by key legislators involved in drafting the regulation. The Recast does not require divulging the company selling the technology or the name of the product that was sold.
Article 26(2) also states that details on implementation of the transparency section of the Recast are to be developed by the European Commission and Council: “The Commission and the Council shall make available guidelines on the methodology for data gathering and processing of the annual report, including the determination of the types of items and the availability of enforcement data.”
In January 2024, the European Commission published guidelines doing just that, detailing the information to be included in the annual report called for by article 26, and the methodology for collecting it.[36] These guidelines are not legally binding on member states, but provide authoritative guidance to states in carrying out their reporting responsibilities under article 26. The guidelines, however, define transparency requirements in ways that undercut the Recast’s objective of ensuring exported dual-use technologies are not used to commit rights violations.
A seemingly small but significant difference, one that applies to all dual-use exports and not simply cybersurveillance technologies, is that the guidelines direct member states to separately list the technologies and the countries to which they were exported, making it often impossible to determine which technologies went to which countries.
The relevant provision of the guidelines reads as follows: “The wording ‘by types of items and by destinations’ in article 26(2) para. 2 … has to be read as requiring [member states] to report authorisations by destinations and, separately, by times of items...”[37]
The Recast itself includes no indication that identification of the technologies and countries to which they were exported are to be listed separately, rather calling on the Commission to include in its report “information on authorisations (in particular number and value by types of items and by destinations at Union and Member State levels)…”
A second difference is that the January 2024 guidelines interpret the transparency requirement of the Recast applicable specifically to cyber-surveillance items in a way that also defeats the aim of shedding light on sales to potential rights abusers. The text of the Recast states: “With regard to cyber-surveillance items, the annual report shall include dedicated information on authorisations, in particular on the number of applications received by item, the issuing Member State and the destinations concerned by those applications, and on the decisions taken on those applications.”
A plain reading of this provision of the Recast, and the reading most consistent with its aims and with statements legislators made about its purposes when it was adopted, is that this information should be presented together such that readers of annual reports know what technologies were transmitted to which countries.
The January 2024 guidelines, however, call for member states to provide only separately listed and aggregated data that would not allow readers to connect specific technology sales to specific recipient countries. The guidelines state that the annual report will include a dedicated section with information on cyber-surveillance items that “will include the number of applications received by Member States as well as the list of all destinations concerned by those applications and the Member States concerned. The wording ‘decisions taken on those applications’ is interpreted as either authorization or denial/prohibition, and this information will be expressed as EU total figure for all the relevant cyber-surveillance items.”
The January 2024 European Commission guidelines thus redefine the type of transparency required by the Recast, separating reporting on what type of technology was exported from the countries to which it was sent, despite explicit indication to the contrary in the text of the Recast that this was not the intended outcome.
By separating data on the items exported and their destinations and by reinterpreting a legal requirement to publish aggregate data instead of specific, per-category information related to cybersurveillance items, the European Commission has made it impossible to connect exports with potential harm, and has undermined one of the key aims of the 2021 Recast.
Misplaced Exporter Confidentiality Concerns Obstruct Meaningful Transparency
In the January 2024 guidelines, the European Commission justifies this reinterpretation of the Recast text, writing that “[t]his interpretation is considered consistent with the need to protect sensitive information under article 26(3) and the need to avoid the risk of undercutting restrictive licensing decisions in the Union.”[38]
A footnote to that paragraph also reads: “Combining data on authorisations by destination and by types of items in one table would very likely lead to significant violations of exporters confidentiality or could undercut restrictive licensing decisions in the EU.”[39]
In a written response to Human Rights Watch, the Commission stated that the 2024 implementation guidelines obfuscate export data because of a concern “that only a limited number of companies were active in exporting such items at the time of the adoption of the Recommendation, thus potentially violating commercial confidentiality or revealing their identity.”
It is not clear how publishing data the Recast specifically requires be made public would violate exporters’ confidentiality, reveal their identity, or undercut restrictive licensing decisions. The provision cited by the Commission, article 26(3), does not limit what the European Commission can do with data properly sent to it under the Recast, in particular what it can or cannot include in annual reports, but instead appears to be intended to make sure data sent from member states to the EU does not run afoul of national transparency laws. The provision reads:
Member States shall provide to the Commission all appropriate information for the preparation of the report with due consideration given to legal requirements concerning the protection of personal information, commercially sensitive information or protected defense, foreign policy or national security information.[40]
This provision resembles language from EU and national transparency legislation that governs access to official documents.[41] EU Member States have similarly worded transparency regulations, where people—sometimes limited to citizens or residents—can request documents from public institutions. These laws outline processes for requesting documents, time periods for response, and processes for appealing decisions.
These transparency laws also outline a series of exceptions to the right to information, under which national or European institutions can legally withhold information in response to document requests. Those exceptions typically relate to the protection of personal information, commercial secrets, and information whose release could harm interests in defense, national security, or a country’s international relations.
By mandating that all information sent from member state licensing authorities to the European Commission be prepared “in due consideration” with legal requirements around the release of protected information, the drafters of the Recast ensured that this information, which is collected only for its inclusion in a public-facing annual report, would not contain any protected information.
Another conceivable basis for requiring the obfuscation of data called for in the January 2024 Commission guidelines stems from more general provisions governing confidentiality of data and statistics, but the relevant EU laws and regulations do not appear to require it either. Article 26(3) also states that “Regulation (EC) No 223/2009 of the European Parliament and of the Council on European statistics applies to information exchanged or published under this Article.” Regulation 223/2009 governs the gathering and reporting of statistics in the European Union. [42] While this regulation contains specific language seeking to prevent the release of confidential data, it’s terms strongly suggest that the type of data the Recast requires EU member states to report do not fall within the definition. [43]
Article 3 of the statistics regulation defines confidential data as “data which allow statistical units to be identified, either directly or indirectly, thereby disclosing individual information.” The same article defines a statistical unit as “the basic observation unit, namely a natural person, a household, an economic operator and other undertakings, referred to by the data.”[44]
In the context of cybersurveillance exports, a statistical unit would presumably therefore include identifying information such as the names of specific companies or people. Such information, while held by national export license authorities, is not included in Recast reporting requirements and member states do not supply it to the Commission per their obligations under the Recast.
The Recast instead calls for reporting of statistical data connecting the exporting member state, the type of technology exported, and the destination country. This information would not qualify as confidential information under Regulation 223/2009.
The January 2024 Guidelines therefore adopt an unjustifiably narrow interpretation of article 26(3), allowing member states and the European Commission to justify keeping confidential what should be publicly available.
Reporting Templates that Limit Transparency
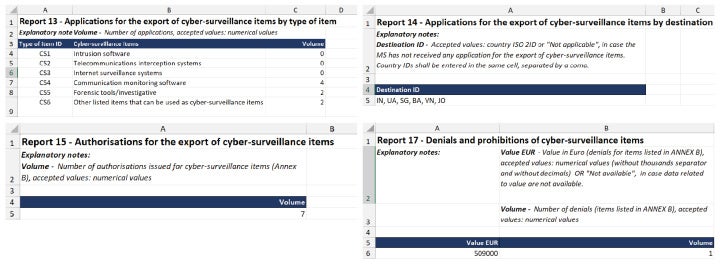
In the January 2024 guidelines, the European Commission also designed the way in which EU member states would carry out their reporting responsibilities related to cyber-surveillance items by providing a series of template spreadsheets for this purpose.
National licensing authorities were instructed to fill out a series of four spreadsheets, corresponding to the total number of license applications per category of cybersurveillance technology, the total number of license applications per destination, the aggregate number of licenses that were authorized, and the aggregate number of license applications denied, as well as the Euro value of these denials.[45]
These spreadsheets present a series of barriers to meaningful transparency on European exports of surveillance technology. Transparency, in this context and per the language and aims of the Recast, would allow readers of annual reports to know what types of technology were sent from which EU member states to which third countries. By separating this data into pieces, the European Commission has limited public ability to scrutinize European exports of surveillance technology.
Another flaw is that spreadsheets ask member states to list only applications—not authorizations—by destination and by type of technology. Only data on authorizations show an actual sale, however, and information on authorizations is provided in aggregate, creating another barrier to the public’s ability to link sales of specific types of technology to specific destination countries, and thus to, accountability. This also hinders exporters and licensing countries from identifying existing risks when those surveillance tools have been connected to harm cases by the end users, and undermines a key element of the recast Dual-use Regulation: the public’s ability to ensure that technology developed in the EU is not being exported to destinations where it could contribute to abuses.
The Commission guidelines also attach a Euro value only to the aggregate number of denied applications. This contributes to a narrative that the EU is missing out on potential sales and exports as a result of the regulation, while not showing the degree to which European companies are profiting from abuses. Including the Euro value of authorized applications would give the public a better view of the technologies EU countries are exporting.
Information in the European Commission Annual Transparency Reports is Insufficient
As of the time of writing, the European Commission had published three annual reports on its implementation of the Dual-Use Recast as well as one “statistical update” document. The first two annual reports, published in November 2021[46] and September 2022,[47] came before the European Commission had finalized its 2024 guidelines.
Both reports include aggregated export data that the European Commission had received from member states in the years prior to the Recast taking effect. The data covered in those reports covers the period from 2014-2020 and tracks aggregate exports of three types of cybersurveillance items. The information published in these reports falls far short of the transparency requirements of the Recast: Presenting export data in aggregate and with no link between exporting country and destination is only capable of showing larger trends across Europe and does not provide the degree of information and accountability called for by the Recast.
The third report[48] was published in January 2025, over one year later than envisioned by the Commission timeline. This was the first annual report published after the Commission released its guidelines, and included slightly more comprehensive export data, from 2022 only. In July 2025 the European Commission published a “statistical update on dual-use export controls,” which included export data from 2023 in the same format as the January 2025 report.[49] Both documents each include aggregate number of exports by type of technology, as well as a map and list showing all of the countries that applied for licenses.
Those lists include many countries with well-documented cases of surveillance harm and related human rights violations. Still, because of how the European Commission has reinterpreted the transparency obligations under the Recast, the data does not connect exporting countries, exported technology, and destination country, or indicate which applications were approved or denied. Because of how the collection and reporting of this data has been structured, it is difficult or impossible to determine the extent to which EU exports are used in committing human rights violations.
Findings from Freedom of Information Requests
In light of the obstacles described above and in an effort to obtain information sufficient for meaningful assessment of whether the Recast is meeting its aims, Human Rights Watch sent freedom of information requests to every EU member state national licensing authority requesting export licensing data as provided to the European Commission per member state obligations under article 26 of the Dual-use Recast.
Seven EU member states[50] responded providing these documents. Another eight export licensing authorities (two of these representing regions in the same country) replied to Human Rights Watch saying that they had not reported any exports of cybersurveillance items to the European Commission in the last five years.[51] The remaining 12 requests were denied and, in one case,[52] ignored.
In most cases where authorities failed to provide information, Human Rights Watch exhausted available national appeals mechanisms in seeking access to the information. In six countries, researchers further appealed the request to the responsible data protection authority, good governance board, or other national transparency oversight institution. One EU country denied Human Rights Watch’s request for the export data as supplied to the European Commission, despite publishing a version of the data on the website of the relevant ministry.[53]
Two member states,[54] as part of the appeals process, asked the European Commission for guidance on how to respond to freedom of information requests for this export data. Human Rights Watch requested and received that correspondence from the European Commission, also via freedom of information request. Those documents include emails from the European Commission providing language for the two national licensing authorities to use in their denials; responses to Human Rights Watch from the two member states were nearly copied verbatim from the Commission guidance.
Human Rights Watch also requested this export data from the European Commission to which member states were required to report. The Commission argued in its response that it cannot provide the export data in question, because, it claimed, the data was confidential, pertained to ongoing decision-making processes, and was restricted because it was sent between member states and Brussels using an encrypted system.
Inside the Responses
The data that Human Rights Watch received from seven EU member states includes evidence indicating widespread exports of surveillance technology from EU countries to over two dozen countries with well-documented histories of surveillance-related rights violations, including hacking, monitoring, extracting, collecting, and analyzing data from digital systems in order to repress activists, journalists, and other critical voices.
The information in these responses represents just a subset of the information shared with the European Commission under the reporting provisions of the Recast. Notably some of Europe’s largest exporters of cybersurveillance items, France, Germany, Greece, Italy, and Spain, denied or, in one case, ignored our access to documents requests. Export licensing authorities in six countries and two regions said they reported zero applications for cybersurveillance items to the European Commission for 2022 and 2023.[55] In its 2025 annual report and in the “statistical update,” both of which contain cybersurveillance export data for 2022 and 2023, the European Commission said it had received data from 14 member states for each year.
The information that Human Rights Watch received, though incomplete, is more detailed than that published in the European Commission’s annual reports. The Commission reports aggregate data received from member states, making it impossible to see on a national level the categories of technology exported and their destinations. By contrast, the number of categories of surveillance technology exported or the number of denials contained in member state responses to Human Rights Watch make it possible in some cases to identify what technologies went to what destination countries, as was the intended outcome of the Recast.
In several instances in which EU member state export licensing authorities refused to provide the information we requested, they asserted that the data requested constituted trade secrets, protected security, or defense information, or was information that could harm their international relations. And yet, in the documents Human Rights Watch was able to obtain, export data is shown in aggregate, and the spreadsheets contain no company names and no technical details. The documents contain only aggregate numerical figures and two letter country codes for destination countries.
Despite the limitations, the information we were able to obtain shows that EU countries have authorized the export of cybersurveillance technology to countries with well-documented histories of surveillance harms, including violations of the rights to privacy and assembly, and the use of surveillance technology against journalists, academics, activists, and others.
Examples of Dangerous Exports: Bulgaria to Azerbaijan and Poland to Rwanda
In many cases, EU member state responses to freedom of information requests allowed Human Rights Watch to identify the country to which a member state exported surveillance technology. In the first example, that of Bulgaria, this is because authorities provided data on authorizations rather than applications; in the second example, that of Poland, it is because there were applications for only one type of technology and no denials. Human Rights Watch focuses on these two case studies because of the large body of information available related to human rights harms and the use of surveillance technology in the destination countries.
Bulgarian Surveillance Exports to Azerbaijan
Data we received shows that one or more companies in Bulgaria exported intrusion software, telecommunications interceptions systems, or both, to Azerbaijan in 2022. Data supplied by the section of the Bulgarian Ministry of Economy and Industry responsible for export licensing[56] confirm exports between 2020-2023 of intrusion software, telecommunications interception, and other types of surveillance technology to authorities in Azerbaijan as well as to Bosnia and Herzegovina, Brazil, Côte d’Ivoire, Dominican Republic, El Salvador, Ghana, Guatemala, Israel, Jordan, Malaysia, Mexico, Mongolia, Morocco, Panama, the Philippines, Serbia, Uganda, the United Arab Emirates, Ukraine, and Vietnam.
Azerbaijan, among other receiving governments, has a long and well-documented history of carrying out surveillance, leading to violations of the right to privacy and other rights, particularly among journalists, activists, and other monitors and critical voices. Azerbaijani authorities regularly carry out arbitrary arrests of activists, journalists, and human rights defenders, regularly interfere with rights to freedom of expression, association, and assembly, and arbitrarily implement laws paralyzing civil society.[57]
Such actions are facilitated by imported surveillance technology, including technology exported by EU member states.[58] In the years prior to Bulgaria exporting surveillance technology to Azerbaijan, security researchers had documented the use of intrusion software and telecommunications interception software by Azerbaijani authorities to surveil journalists and civil society.[59]
In Bulgaria, the surveillance company Circles exports its products to customers across the globe. Circles reportedly sells a product that exploits vulnerabilities in the international telecommunications infrastructure which, according to security researchers, allows users to track mobile phone users, intercept their communications and, in some cases, infect their devices with spyware. [60] Circles is affiliated with NSO Group, the Israel-based company that developed and sells Pegasus spyware. Circles reportedly merged with NSO in 2014, when U.S. private equity firm took control of both for a total of $250 million. [61] Circles reportedly held a license to export from Bulgaria that expired in 2023, and current public data on the Bulgarian Ministry of Economy and Industry's website indicates that the company has received licenses to export from Bulgaria from 2023-2028.[62]
Regarding Azerbaijan, a consortium of security researchers has found “substantial” evidence “suggesting that Azerbaijan is a Pegasus customer” and used the software to hack the devices of victims in Armenia, including journalists, activists, academics, a UN worker, and others.[63] That consortium found Azerbaijani or Azerbaijan-linked servers pointing to Azerbaijan as a likely Pegasus customer. The Citizen Lab, security researchers affiliated with the University of Toronto, also found that Azerbaijan likely used Pegasus spyware to infect the devices of members of Armenian civil society during the 2023-armed conflict between Azerbaijan and Armenia over Nagorno-Karabakh.[64]
There is no evidence in the export data provided by the Bulgarian Ministry of Economy and Industry to Human Rights Watch that any Circles' products were exported to Azerbaijan because the data does not provide information on companies involved. However, Circles is currently registered to export from Bulgaria. Furthermore, there is substantial evidence of surveillance-related harm committed by Azerbaijani authorities and of companies exporting surveillance technology from Bulgaria since that harm was made public and since the recast Dual-use Regulation came into effect.
This case study highlights two shortcomings of the implementation of the Recast: First, that surveillance technology was sent to a government with a record of using such technology to violate rights; and second, the transparency of data available is insufficient to understand what was actually exported.
In response to written questions to the Bulgarian Ministry of Economy and Industry, the ministry responsible for dual-use export licensing, the minister wrote that “[e]xports that contradict the country's national, European and international commitments, including with regard to the protection of human rights, are not allowed” and that “[t]he Ministry maintains a consistent policy of zero tolerance for abuses and strictly monitors compliance with the established rules.” The ministry would not discuss the details of its exports to Azerbaijan, citing commercial secrecy.
Representatives for Circles and NSO Group did not respond to written requests for comment by the time of publication.
Polish Surveillance Exports to Rwanda
Export data provided by the Polish Ministry of Entrepreneurship and Technology shows that a Polish company or companies sold and exported telecommunications interception systems to Rwanda in 2023. While the data does not identify which company or specific product was sold, or the end user in Rwanda, the Rwandan government’s track record of digital surveillance of dissidents and journalists, heightens the risk of exports being used to violate rights.
Rwandan authorities repress political opposition domestically and abroad, and few journalists, civil society activists, or opposition members dare speak out publicly against the government or on topics it views as sensitive.[65] Authorities have also responded forcefully and often violently to criticism, deploying a range of measures to deal with real or suspected opponents, including extrajudicial killings, enforced disappearances, torture, political prosecutions, and unlawful detention, as well as threats, intimidation, harassment, and physical surveillance.[66]
Digital surveillance forms an important part of this repression both inside Rwanda and among the diaspora worldwide. In Rwanda a new law adopted in 2013 greatly expanded surveillance powers, in particular authorities' ability to intercept and monitor communications for arbitrary reasons and with little legal oversight. The penal code, revised in 2018 also expands the criminalization of online speech. Rwandan authorities have also used Pegasus spyware against journalists and dissidents since at least 2017 and reportedly have targeted thousands of activists, journalists, and politicians with spyware.
In response to written questions, the Polish Ministry of Economic Development and Technology wrote that Poland has a multi-agency process for human rights assessments of dual-use exports where “the risk of possible misuse of goods in a third country is examined, including the risk of the goods being used to violate human rights. During the analysis of the cases in question, no such risk was identified, resulting in the issuance of an export license for these goods to Rwanda”
The Rwandan ministries of Justice and Interior did not respond to written questions by the time of publication.
Some Surveillance Technology Falls Through the Cracks: Case of Sweden
The Swedish export licensing authority, called the Inspectorate of Strategic Products (ISP), confirmed to Human Rights Watch that the institution reports limited data to the European Commission per Sweden’s reporting obligations under the recast Dual-Use Regulation.
In response to an access to information request, the ISP provided what it said was all of the information sent from Sweden to the European Commission per its reporting obligations under article 26 of the Recast. This data includes only one of the four required spreadsheets for each year. The spreadsheet data only confirmed that the authority issued denials or prohibitions in 2022 and 2023, by listing a total of zero applications or authorizations for cybersurveillance items in 2023 and withholding any information on applications or authorizations from the Commission in 2022.
In response to questions about the limited data provided, the ISP stated that it does not supply complete information to the European Commission “due to secrecy reasons,” that it supplied to Human Rights Watch “the same information as [the ISP] have sent to the European Commission,” and that “[a]ny information that has been omitted in the reporting has been done so in accordance with article 26(3) in Regulation 2021/821.”
Nevertheless, data from a third-party trade data aggregator shows exports of surveillance technology from Sweden covering those years. For example, the company MSAB, a European developer of universal forensic extraction devices (UFEDs) and Europe’s main competitor to the Israeli-based company Cellebrite, exports their digital forensic extraction tools throughout the world from Sweden.
MSAB’s products are capable of bypassing mobile device encryption and passcodes without the user’s consent, and extracting data including messages, contacts, photos and video, call and location logs, and login tokens and passwords for online services.[67] Still, as the Inspectorate for Strategic Products in response to written questions explained, these devices may not be captured by the controls on forensic/investigative tools and tools used to perform cryptanalysis contained in the EU Dual-use list, because they fall under an exception. Specifically, the ISP pointed to the section in the 2024 Commission guidelines, which says that tools not ‘specially designed’ for covert surveillance do not fall under the definition of cyber-surveillance items..
This loophole means that surveillance technology which functionally meets all criteria that would lead it to be regulated as a cybersurveillance item, in practice falls outside of the types of technology that the regulation captures.
As an example, according to aggregated export data, MSAB exported UFED products to India every year from 2023. This is despite Indian authorities being implicated in using spyware to hack activists’ and journalists’ devices at least since 2019, amid an ongoing crackdown on freedom of speech and assembly. In 2023, India passed its first data privacy law that enhances the power of the state to conduct surveillance, without adequate safeguards or oversight mechanisms.
While Human Rights Watch has not found specific evidence that MSAB’s products were used to crackdown on dissent in India abused in either country, the evidence of these exports and the fact that Swedish authorities do not legally have to report them to the European Commission suggests that the Recast is not doing enough to require EU member states to carry out due diligence and report exports of cybersurveillance technology.
The Swedish Ministry of Foreign Affairs referred written questions to, the Inspectorate for Strategic Products whose full response can be read in Annex IV.
The Indian Ministries for Railways, Information and Broadcasting and Electronics and Information Technology, of State for the Ministry of Commerce and Industry, and of Electronics and Information Technology, and representatives for MSAB did not respond to written questions by the time of publication.
Human Rights Standards
As is evident from the rationale behind the Recast, the obligation to regulate the sale and export of surveillance technology stems from the inherent threat to the right to privacy the existence of such technology poses, as well as the many serious violations of other rights - from freedom of expression and assembly, to the right to life and freedom from torture - that can flow from its use, particularly when used to target individuals and communities on a discriminatory basis. The United Nations High Commissioner for Human Rights has published a series of thematic reports on the impact of the digital age on the right to privacy and other rights, that helps identify the impact on rights of surveillance technology and the relevant legal standards and best practices that govern its use.[68]
Mitigating Extraterritorial Abuses
In the context of concerns about surveillance technologies and human rights violations, and noting that their global trade makes them “easily accessible for a broad range of uses, including to carry out and facilitate unlawful and arbitrary surveillance”, the United Nations High Commissioner for Human Rights has on many occasions addressed the need for adequate export control regimes for the sale of surveillance technologies. The High Commissioner and other UN independent human rights experts have repeatedly called on states to adopt “robust export control regimes” to prevent the sale of surveillance technologies when there is a risk that they could be used for violating human rights.[69]
They have called on states to ensure that an assessment of the risk of human rights violations and abuses facilitated by surveillance technology is a key factor in decisions on export licenses,[70] and the High Commissioner has supported a call by the Special Rapporteur on the right to freedom of opinion and expression for governments to impose a moratorium on granting export licenses for surveillance technologies until
a) the use of those technologies can be technically restricted to lawful purposes that are consistent with human rights standards, or
b) it can be ensured that those technologies will only be exported to countries in which their use is subject to authorization – granted in accordance with due process and the standards of legality, necessity and legitimacy – by an independent and impartial judicial body.[71]
To meet their human rights obligations, it is not enough that states adopt such controls, but that the controls are monitored and enforced to ensure they achieve their preventative purpose.
This report shows that the EU control system has failed to prevent dangerous surveillance technologies getting into the hands of those with track records of using them to violate rights. The right of access to information, which is an element of the Recast, should serve to enable journalists and civil society, to identify if and how that is happening and to act as a mechanism for public accountability.
Right of Access to Information
The right of access to information is well established in international human rights law as a fundamental part of the right to free expression, and guarantees individuals, groups, and companies the right to obtain information from public bodies while also obliging those public bodies to facilitate access to information through responses to requests and proactive publication.
Article 10 of the European Convention on Human Rights (ECHR), to which every EU member state is a party, provides that the right to freedom of expression includes “the freedom to receive and impart information and ideas without interference by public authority”, subject only to those restrictions that are “prescribed by law and are necessary in a democratic society, in the interests of national security, territorial integrity or public safety, for the prevention of disorder or crime, for the protection of health or morals, for the protection of the reputation or rights of others, for preventing the disclosure of information received in confidence, or for maintaining the authority and impartiality of the judiciary.”[72]
Over time, the European Court of Human Rights has recognized that the notion of “freedom to receive information” embraces a right of access to information.[73] The Court affirmed the right of access to information in the leading case of the Hungarian Helsinki Committee v Hungary emphasizing that the media and civil society organizations need access to information to perform their “watchdog” function, part of which involves imparting the requested information to the public, contributing to the public debate.[74] While the Court maintains that the European Convention does not impose a positive obligation on states to collect and disseminate information of their own motion, it has set down that there are limited circumstances that justify refusal to grant access to information that is ready and available, and to which people are legally entitled.
The Court also observed that other international human-rights bodies have also linked watchdogs’ right of access to information to their right to impart information and to the general public’s right to receive information and ideas.[75] When public bodies refuse to release relevant documentation, unless fully justified as necessary and proportionate to fulfil a legitimate aim, they violate the right of access to information.[76]
At the EU level, article 15 of the Treaty on the Functioning of the European Union (TFEU), and article 42 of the Charter of Fundamental Rights of the European Union provide that citizens have “a right of access to documents of the EU institutions, bodies, offices, and agencies, regardless of their medium”. The right coexists with the principle of transparency among EU institutions. Article 10 of the Treaty on European Union (TEU), states that “decisions shall be taken as openly and as closely as possible to the citizen,” and article 11 provides that individuals and associations should have the “opportunity to make known and publicly exchange their views in all reasonable of Union action.”
The right of access to information is further operationalized in Regulation 1049/2001 which gives the public a right to the “widest possible access” to documents, reinforcing a presumption of transparency tied to the democratic credentials of the EU institutions. The European Court of Justice’s jurisprudence makes clear that the right of access to information is a mechanism to ensure participation, accountability, and institutional legitimacy are maintained within the EU’s constitutional order. While exceptions to disclosure are explicitly provided for in Regulation 1049/2001, the Court has emphasized they must be interpreted and applied strictly. It has made clear that the burden is on institutions to establish, in the case of full or partial refusal of documents, “how access to that document could specifically and actually undermine the interest protected by the exception.”
Article 19 of the International Covenant on Civil and Political Rights (ICCPR), to which every EU member state is also a party, guarantees freedom of expression in similar terms to article 10 of the ECHR. It provides that the right to freedom of expression “shall include the freedom to seek, receive and impart information and ideas of all kinds, regardless of frontiers...”. Restrictions on this right “shall only be such as are provided by law and are necessary: (a) For respect of the rights or reputations of others; (b) For the protection of national security or of public order (ordre public), or of public health or morals.”
The UN Human Rights Committee, which oversees implementation of the ICCPR, in its General Comment No. 34 affirms the right to request information “held by a public body, regardless of the form in which the information is stored, its source and the date of production,” from any government entity or authority, or other entity “carrying out public functions.”
The tension between the right to free expression and access to information on the one hand, and national security on the other, has been the subject of much inquiry by courts, international bodies, and scholars. A group of experts in international law, national security, and human rights issued the Johannesburg Principles on National Security, Freedom of Expression and Access to Information on October 1, 1995. Over time, these Principles have come to be widely recognized as an authoritative interpretation of the relationship between these rights and interests, reflecting the growing body of international legal opinion and emerging customary international law on the subject.
The Johannesburg Principles state that restrictions on access to information should be permitted only when “the government can demonstrate that the restriction is prescribed by law and is necessary in a democratic society to protect a legitimate national security interest” (Principle 1.1, section d). According to the Principles, the burden of demonstrating the validity of the restriction rests with the government.
Right to Privacy
Article 8 of the ECHR provides that, everyone has the right to “respect for his private and family life, his home and his correspondence” and that there shall be “no interference by a public authority” except such as is “in accordance with the law and is necessary in a democratic society in the interests of national security, public safety or the economic well-being of the country, for the prevention of disorder or crime, for the protection of health or morals, or for the protection of the rights and freedoms of others.”
The European Court of Human Rights has adjudicated many cases in which the use of surveillance technology has been challenged as a violation of the right to privacy and other rights, and through its caselaw, starting with the Weber and Saravia v. Germany, has developed a robust framework for assessing if its use is compliant with the convention.[77] Starting from the premise that surveillance is always an interference with the right to privacy, the Court has set down that to be in accordance with the law, the domestic law “must not only be accessible and foreseeable in its application” but there must be “adequate and effective safeguards and guarantees against abuse”.[78]
According to the court’s caselaw the minimum requirements that should be set out in law authorizing use of mass surveillance, including powers of interception, include:
i. the nature of offences which may give rise to use of such powers;
ii. a definition of the categories of people liable to be subject to their use;
iii. a limit on the duration of their use;
iv. the procedure to be followed for examining, using and storing information obtained;
v. the precautions to be taken when communicating the information to other parties; and
vi. the circumstances in which information may or must be erased or destroyed
vii. the procedures and modalities for supervision by an independent authority of compliance with the above safeguards and its powers to address non-compliance;
viii. the procedures for independent ex post facto review of such compliance and the powers vested in the competent body in addressing instances of non-compliance.[79]
The Court has also made clear that states must not only refrain from unlawful surveillance but protect individuals against privacy intrusions by private actors, including companies handling large-scale personal data.
Article 17 of the ICCPR is similar to article 8 ECHR and provides that “[n]o one shall be subjected to arbitrary or unlawful interference with his privacy, family, home or correspondence,” and “[e]veryone has the right to the protection of the law against such interference or attacks.” Correspondence should be understood to encompass all forms of communication, both online and offline.[80]
The Human Rights Committee has interpreted “arbitrary interference” as follows:
The expression “arbitrary interference” is also relevant to the protection of the right provided for in article 17. In the Committee’s view the expression “arbitrary interference” can also extend to interference provided for under the law. The introduction of the concept of arbitrariness is intended to guarantee that even interference provided for by law should be in accordance with the provisions, aims, and objectives of the Covenant and should be, in any event, reasonable in the particular circumstances.[81]
Limitations on the right to privacy similarly must be prescribed by law, necessary to achieve a legitimate aim, and proportional and narrowly tailored to achieving the aim.[82] The special rapporteur on freedom of expression has stated that:
Communications surveillance should be regarded as a highly intrusive act.… Legislation must stipulate that State surveillance of communications must only occur under the most exceptional circumstances and exclusively under the supervision of an independent judicial authority. Safeguards must be articulated in law relating to the nature, scope, and duration of the possible measures, the grounds required for ordering them, the authorities competent to authorize, carry out and supervise them, and the kind of remedy provided by the national law.[83]
To be prescribed by law, limitations on the right to privacy must meet “a standard of clarity and precision that is sufficient to ensure that individuals have advance notice of and can foresee their applications.”[84] As the special rapporteur on human rights and counterterrorism explains, these principles apply even where the stated aim of surveillance is countering terrorism: “there must be no secret surveillance that is not under the review of an effective oversight body and all interferences must be authorized through an independent body.”[85]
Responsibilities of Companies
Companies have a responsibility to respect human rights. This principle is reflected in the United Nations “Protect, Respect, and Remedy” Framework and the UN Guiding Principles on Business and Human Rights, which are widely accepted by companies and governments. The responsibility to respect requires that companies undertake credible human rights due diligence and mitigate human rights risks so that their operations do not facilitate or exacerbate human rights problems. The UN Guiding Principles foresee that companies involved in the development, sale and export of surveillance technologies, should as a minimum:
Conduct rigorous due diligence and put in place procedures to identify, prevent, mitigate, and account for how they address their impacts on human rights.
Employ human rights impact assessments to identify circumstances when freedom of expression and privacy may be jeopardized or advanced and develop appropriate risk mitigation strategies. Such assessments should occur in relation to designing and introducing new technologies, entering a new market, taking on business partners, or committing to business contracts or license agreements.
Seek clarification as to the end use and end user of the technology or service, and procedures to prevent use of a company's technology or services to facilitate human rights abuses.
Put in place processes to enable remediation of any adverse human rights impacts they cause or to which they contribute.
The UN Special Rapporteur on freedom of opinion and expression, his 2019 report on the adverse effect of the surveillance industry on freedom of expression, also provides guidance to companies on how to fulfil their responsibilities. [86] Specifically he calls on private surveillance companies to “integrate human rights due diligence processes from the earliest stages of product development and throughout their operations”, and “put in place robust safeguards to ensure that any use of their products or services is compliant with human rights standards”. He further states that when “companies detect misuses of their products and services to commit human rights abuses, they should promptly report them to the relevant domestic, regional or international oversight bodies. They should also establish effective grievance and remedial mechanisms that enable victims of surveillance-related human rights abuses to submit complaints and seek redress.”[87]
Acknowledgments
This report was researched and written by Zach Campbell, senior surveillance researcher at Human Rights Watch. The report was edited and reviewed by Deborah Brown, deputy director, Technology, Rights and Investigations division, and Joseph Saunders, deputy program director. Specialist review was provided by Kartik Raj, senior researcher, Europe and Central Asia division; Clementine de Montjoye, senior researcher, Africa division; Etienne Maynier, security technologist, Information Security and Technology division; Hélène de Rengervé, senior advocate, Måns Molander, Nordic director and Christina Abdulahad, senior coordinator, Advocacy. Legal review and support were provided by Aisling Reidy, senior legal advisor, Legal and Policy. Editorial assistance was provided by Ekin Ürgen, research assistant, Technology, Rights and Investigations division.
External research support was provided by FIND.ngo.
Additional expert review was provided by Fionnuala D. Ní Aoláin, former special rapporteur on counter-terrorism and human rights, and regents professor, University of Minnesota Law School; and Mark Bromley, director of the dual-use and arms trade control programme at the Stockholm International Peace Research Institute (SIPRI).
Travis Carr, publications manager, provided production coordination; Win Edson, senior motion graphic designer, produced the videos accompanying the report. Data visualizations were provided by Christina Rutherford, senior web manager, and Carlos Albaladejo i Moreno, a consultant.
Illustrations were provided by Glenn Harvey.
Human Rights Watch would like to thank the external partners who provided support and guidance with freedom of information requests to European Union institutions and member states: In Bulgaria, Stephan Anguelov, attorney at law, Access to Information Programme, and Maria Cheresheva, journalist; in Greece, Stephanos Loukopoulos, director and co-founder, Vouliwatch; in Slovenia, Domen Savič, general manager, Citizen D; and regarding requests to European Union institutions, Luisa Izuzquiza, head of EU office, FragDenStaat.